Lists of frequently asked questions
General questions
Do viruses exist for mobile devices?
Malignant applications for mobile OSs are the fastest growing malware segment. As popularity of an OS is growing among users, so does the interest in it on the part of intruders, whose main goal is to get money. The number of threats to Android increases most rapidly.
Do dangerous malignant programs exist for Android?
Yes, there are and their number is growing. Android.SmsSend Trojan horses that emerged as early as in 2010 are the most common threats to the OS. They are designed to send SMS messages at premium numbers and sign up subscribers to various services.
Mobile banking Trojans are designed to intercept SMS messages, steal mTAN-codes and pass them to criminals who perform various financial transactions with accounts of unsuspecting victims (for example, make online purchases) pose an extreme danger. Android.SpyEye.1 is a banking Trojan for Android OS.
Such malware as Android.MailSteal.1.origin, Android.Maxbet.1.origin, Android.Loozfon.origin and Android.EmailSpy.origin. steal e-mail addresses from devices' address books and send them to a remote server, so that attackers can carry out spam mailings.
Why must your employees' personal mobile devices be protected in addition to their corporate computers, especially if they work with company finances (e.g., bookkeepers)?
While out of the office, employees are not protected from hackers, applications they use may have vulnerabilities, their computers and mobile devices can be infected with viruses and Trojans that steal banking and payment system access passwords and money from bank accounts.
Employees regularly connect to the company's network via their device, and thus put confidential data and money at risk—not only their personal assets but corporate too. Incidents when malware gets onto a local network from personal devices, including handhelds, account for up to 70% of intrusions.
In addition, banks often send SMS confirmations to maintain security of transactions. There are malignant programs that can modify such confirmation messages. An anti-virus guarantees that incidents when money is stolen from accounts will never be concealed.
I never install malware! How can my handheld get infected?
You don't need to install anything — just visit a compromised web-site. And it won't necessarily be a site with objectionable content — from intruders' point of view, hacking news portals is much more useful. News sites are the most visited ones on the Internet. They usually do not cause any suspicion among users or system administrators from companies which do not block access to such sites. That's why news portals are a very attractive field of operation to intruders. By Spreading malware through such sites, they can cause damage to a huge number of users and companies.
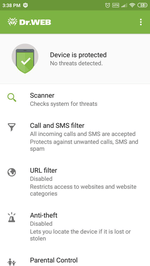
What does Dr.Web for Android protect against?
Dr.Web for Android protects from viruses and other malicious programs that may steal or damage information stored on the mobile device. It prevents viruses from getting and running on a mobile device.
Note: Dr.Web for Android can only protect mobile devices and its virus databases are different from those used by the anti-virus maintaining security of desktops and laptops. To protect a computer, use corresponding products from Doctor Web.
Does the anti-virus affect my device’s performance?
Dr.Web anti-virus occupies about 1 MB in the device memory. Only the file monitor that keeps track of the system processes resides in the memory at all times. The monitor requires a certain amount of resources, but it has no noticeable effect on overall performance.
How can I know what Dr.Web for Android I’m using?
In the top-right corner of the main application window, click on the menu icon, and select About.
On the newly appeared page, you'll find information about the name and version of the Dr.Web solution you’re using to protect your device.
The name of your Dr.Web product can also be found in the License Manager on Doctor Web’s site.
If you inadvertently downloaded Dr.Web for Android Light instead of Dr.Web Security Space for Android, download a free 14-day trial for the full version (the trial is issued during installation) from Doctor Web’s site. You can also download the full version of Dr.Web from Google Play.
What do I do if I inadvertently downloaded Dr.Web for Android Light instead of Dr.Web Security Space for Android?
Download a free 14-day trial for the full version (the trial is issued during installation) from Doctor Web’s site.
You can also download the full version of Dr.Web from Google Play.
How can I check whether my Dr.Web license is valid?
In the top-right corner of the main application window, click on the menu icon, and select License.
On the newly appeared page, you can find out who owns the license and when the license expires.
The validity period of your Dr.Web license can also be viewed in the License Manager on Doctor Web’s site..
My anti-virus detected threats and removed them, but they’ve reappeared. What should I?
The main signs that malicious behaviour is occurring in the system area are as follows:
- The multiple appearance of the same threats in the same areas, even after the anti-virus has removed them. Threats usually reappear after a device reset.
- Notifications in Dr.Web Security Auditor.
Due to the specific features of the Android OS, it's impossible to employ the standard features of ANY anti-virus to neutralise trojans in the system memory because, just like any other application, an anti-virus installed on a non-root device does not have administrative privileges: Dr.Web can detect malicious programs that get into the Android system directory, but it is not authorised to remove them. In addition, the quarantine option is not available for them (or for any other installed application).
To close firmware vulnerabilities and neutralise threats in /system, you can stop or disable some system applications. This will not eliminate a threat completely, but it will neutralise it until you can remove it permanently.
To stop an application: in the list of installed applications on the screen Settings → Applications, select the application that has been determined to be a threat and then on the screen containing the information about it, click on the Stop button.
This action will need to be repeated every time you restart the device.
Disable the application via the device settings: in the list of installed applications on the screen Settings→ Applications, select the application that has been determined to be a threat and then on the screen containing the information about it, click on the Disable button.
If your device is rooted (with superuser privileges that allow you to make any type of change you want, including to the firmware) and an application can be removed without disrupting device operation or cured, you will see the corresponding option in the anti-virus's interface.
With root access enabled, you can also try to remove malicious applications with the help of special third-party utilities.
In some cases, configuring root access may lead to the device manufacturer denying to provide you with warrantied maintenance.
If your device has custom firmware, you can restore the device manufacturer’s official software on your own or contact the service center. If you are using the device manufacturer’s official software, try to contact the manufacturer to get more information about this application.
If the manufacturer recommended that you update the firmware, before doing this, make a backup of all your user data and then do a reset to the factory settings.
To disable information about threats in system applications that cannot be removed without disrupting device operation, tick the System Applications box in the Settings section → General settings → Additional options.
We also recommend that you read the Anti-virus Times issue dedicated to this topic — System business. Please refer to the issue Firmly rooted to know how trojans can find their way into firmware.
How can I check whether the anti-virus is running?
Start Dr.Web for Android. In the subsequent window go to the SpIDer Guard section and check if the Monitor is enabled and protects the system message is displayed. If it is, the anti-virus protects your device. If the message is Monitor disabled, the monitor is not running. Tap the monitor indicator button.
How can I scan my device for viruses?
To scan your mobile device for viruses, launch Dr.Web for Android, and tap Scanner. In the next window, specify the scan mode.
- Quick scan. The anti-virus scans only files of installed applications. The fewer there are applications, the sooner the express scan will be completed.
- Full scan. All files on your mobile device are scanned.
- Custom scan. Scan only certain files or folders for viruses. To run a custom scan, select objects you want to scan and tap the Scan button.
Abort scan at any time by tapping Abort.
How can I view anti-virus statistics?
Launch Dr.Web for Android and select Statistics. The statistics window displays the number of processed files and information about all actions performed by the anti-virus components. It is possible to reset the statistics (Menu→Clear statistics), or save the log to a file (Menu→Save log).
A virus warning has appeared. What should I do?
Tap on the Dr.Web icon on the notification panel. In the succeeding window you will see all the available information about the threat. Tap on this message, then select the desired action: delete the file, place it into the quarantine, or ignore the warning.
Warning! It is not recommended to choose the Ignore option! If you believe that the anti-virus has made a mistake, select Quarantine and after that send the file to Doctor Web for a detailed analysis.
What do I do if Dr.Web can’t remove a malicious program?
Dr.Web cannot remove malware if the device firmware is infected. Contact the device manufacturer’s authorised service center to get your device’s firmware replaced.
What does SpIDer Guard do?
SpIDer Guard is designed to constantly protect mobile devices against viruses and other threats. It loads into the memory upon Android start-up and scans all files accessed by a user or the system in real time.
Nothing found